OMI AI PLATFORM
Remember Every Moment,
Talk to AI and Get Feedback
Join the #1 open-source AI wearable community
Build faster and better with 3900+ community members on Omi Discord
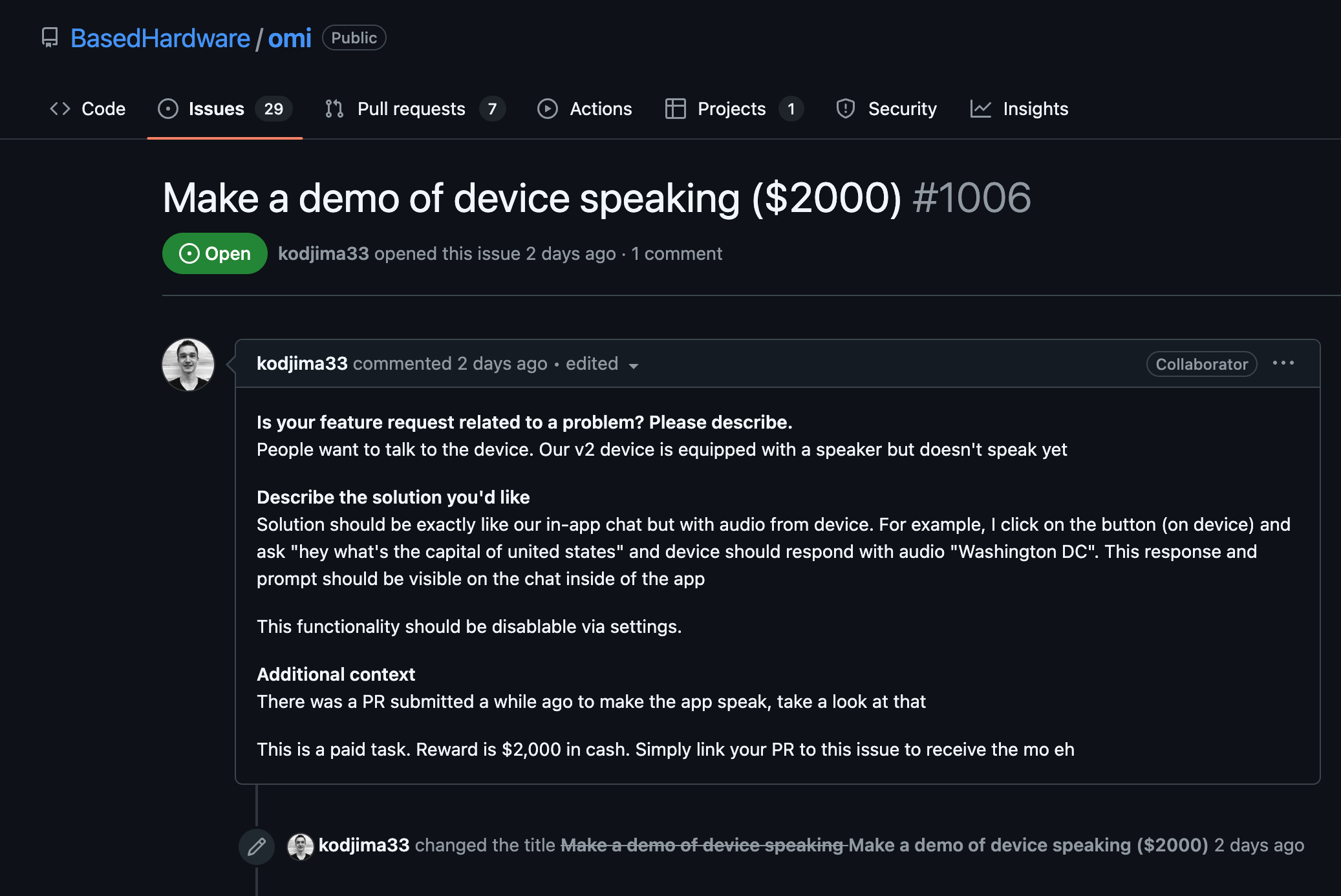
Participate in hackathons to expand the Omi platform and win prizes

Participate in hackathons to expand the Omi platform and win prizes
Get cash bounties, free Omi devices and priority access by taking part in community activities
OMI NECKLACE + OMI APP
First & only open-source AI wearable platform












Omi 開発キット 2
商品が見つかりません
Omi Dev Kit 2: 新しいレベルのビルド
主な仕様
人々が言うこと
OMIネックレス:開発キット
脳を次のレベルへ
商品が見つかりません







